
SCAM ALERT!
A friend I have known since my university days recently came dangerously close to falling for a phone scam. Nothing unusual there, you might think. However, this victim was a hard-headed businessman, the last person you would expect to be caught out by scammers. I began to think about the number of people I knew who had been targeted in this way.
Generally, the victims of these scams are NOT poor decision-makers. They may, like my friend, have successful business or professional careers, but something makes them unduly open to persuasion. Modern life is increasingly complicated and the information overload seems to get a greater every day. We navigate through its using all sorts of shortcuts and rules-of-thumb. Scammers take advantage of these processes to catch their targets off-guard. Which means that no one is immune to being scammed. We need to be on our guard: if something sounds like a scam it probably is one.
The subconscious mind can be exploited in different ways. Scammers know about many of the techniques that can help people to take irrational decisions. These include allowing them to visualise future outcomes, motivating them to make over-hasty decisions, among many other methods. Many scams target people who do not have enough technical knowledge to understand how some things work. When a person has less knowledge about something it becomes much easier for a plausible scammer to drag him into their trap.
Wikipedia defines Emotional intelligence (EI) as: “the capability of individuals to recognize their own, and other people’s emotions, to discern between different feelings and label them appropriately, to use emotional information to guide thinking and behaviour, and to manage and/or adjust emotions to adapt environments or achieve one’s goal(s).” Which is a long-winded way of saying that, when dealing with strangers (particularly on the telephone) you need a very strong empathetic sense of what is going on in the current transaction. Scammers also use emotion intelligence to make us comply and to “feel safe”. Perhaps this explains why so many technically-oriented professionals fall into the trap.
Saddest thing of all, it is good people who make the easiest targets. Some people assume that all people are “good”; usually the ones who really are “good” think that way. By believing that everyone out there is like them, they respond to scammers without suspicion. I would put my friend in this category, although he had enough life-experience to smell a rat when his caller told him that he was due a credit from BT Openreach for which they would need bank details.
Forgive me if I am preaching to the converted but I treat all cold calls whether by telephone or email or any other method with deep rooted suspicion, but that might be because I am a tight-fisted Yorkshireman, a cynical bastard, or probably both. Whichever way it might be I have learned to respond to cold calls by telephone either by telling the caller that, when I want the goods or services they are purporting to sell, I will go looking for them myself or, if I am interested, I tell them that I am too busy to talk at the moment and ask them for their telephone number so that I can ring them back when I am free. It is amazing how many callers hang up at this point.
If you are targeted by phone, including texts, or by email or are the victim of any kind of cybercrime, please report it immediately to Action Fraud any time of the day or night using their online fraud reporting tool: www.actionfraud.police.uk/report_fraud, or by calling 0300 123 2040. Your local police might also have their own cybercrime unit. The more information the police receive the more likely they are to put a stop to the scammer.
As an object lesson:
- This was a BT Openreach scam, masquerading as a cold call about broadband speed.
- The caller installed Team Viewer on my friend’s PC ostensibly to check broadband speed.
- He did ask for ID and the credentials offered were very plausible. For example: everything that was shown was branded as “BT Openreach”.
- The scammer asked my friend to type values into terminal.
- The calling telephone number was within the UK.
Carefully prepared and expertly executed. Unlike a scam that was visited on a friend in the USA who got an email from “Smith & Weston”! We cannot rely on scammers to make obvious mistakes these days; they have learned.
One lesson we can learn is not to let anybody take control of your computer unless you have contacted them and asked them to – for example – run diagnostics. Otherwise nobody has any legitimate reason to take over control of your computer and you do not have to type in any values if you are uncomfortable doing so.
A suggested immediate action drill on finding yourself in this situation:
- Break the Internet connection at once, and I mean physically. Pull out the cable or switch off the router.
- Put your virus protection and related security software on a deep scan.
- Phone your bank to have them monitor your account(s).
- Phone your payment card providers (there is usually an emergency number printed on the back of each card) so that they can block any suspect transactions.
- Contact your dealer, tech support number or any other support you have available to you, tell them what has happened and follow their instructions. Most suppliers and manufacturers have a help line. This may involve taking your machine in or calling out an engineer to thoroughly diagnose the extent of the damage done.
- Lodge an incident with the police (see above).
- When you are back on line send an email to everyone in your contact book to tell them to report any unusual messages they receive from you. Do not be embarrassed to admit that there has been an attempt to scam your account; you are acting decisively to clear up after it.
One last word: I keep the emergency numbers (tech support, BT, police, bank etc.) on a card that goes everywhere with my laptop. I have never had to use it but I am easier in my mind knowing that I have everything in one place if I do fall victim.
Related Post
CYBER-SECURITY MUST BE...
CYBER-SECURITY MUST BE TOP-DOWN AND ALL-PERVADING There is a dawning suspicion among both...
- March 30, 2016
- By amdsconsultants_l7b8il
- Cybercrime
DIGITAL TRANSFORMATION...
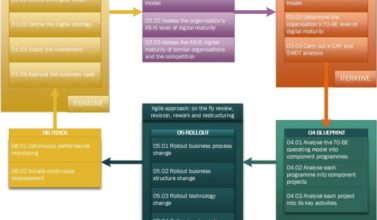
DIGITAL TRANSFORMATION STRATEGY FRAMEWORK Ask a consultant to describe “digital...
- July 11, 2018
- By amdsconsultants_l7b8il
- Business Continuity Management
Archives
Categories
- Business Continuity
- Business Continuity Management
- Change Management Consultant
- Cyber Security
- Cybercrime
- Data Protection
- Data Security
- Defence Test & Evaluation
- Excellence in Customer Service
- Lean Six Sigma
- Marketing
- Organisational Culture
- Organisational Design
- Pro Bono
- Product Review
- Project Management
- Public Sector Procurement
- Requirements Engineering
- Requirements Management
- Six Sigma
- Soft Skills
- Teamwork




Leave a Comments